Popular hacking group LulzSec, responsible behind hacking the PSN, have announced that they will be retiring, exactly 50 days after forming the group.
The group have released a farewell statement urging all its supporters to support the AntiSec movement, saying:
“Again, behind the mask, behind the insanity and mayhem, we truly believe in the AntiSec movement. We believe in it so strongly that we brought it back, much to the dismay of those looking for more anarchic lulz. We hope, wish, even beg, that the movement manifests itself into a revolution that can continue on without us. So with those last thoughts, it’s time to say bon voyage. Our planned 50 day cruise has expired, and we must now sail into the distance, leaving behind – we hope – inspiration, fear, denial, happiness, approval, disapproval, mockery, embarrassment, thoughtfulness, jealousy, hate, even love. If anything, we hope we had a microscopic impact on someone, somewhere. Anywhere.â€
LulzSec did go out with a bang however, the group claims they have obtained 50,000 passwords of Gaming forum members, 55,000 Battlefield Heroes Beta users’ data, AT&T Internal Data, 200,000 hackforums member data, AOL internet data and more. Read the full statement here.
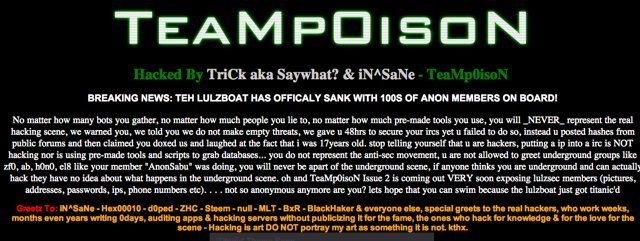
Previously, the group were said to be taken down by a 17-year-old member of a hacking group named TeaMp0isoN_. While gaining attention through their acts of “hackery,†the group annoyed some members of the hacking community, as a member of hacking group TeaMp0isoN_ hacked the site of a LulzSec member, posting the following message (after defacing the site):
BREAKING NEWS: TEH LULZBOAT HAS OFFICALY SANK WITH 100S OF ANON MEMBERS ON BOARD!
No matter how many bots you gather, no matter how much people you lie to, no matter how much pre-made tools you use, you will _NEVER_ represent the real hacking scene, we warned you, we told you we do not make empty threats, we gave u 48hrs to secure your ircs yet u failed to do so, instead u posted hashes from public forums and then claimed you doxed us and laughed at the fact that i was 17years old. stop telling yourself that u are hackers, putting a ip into a irc is NOT hacking nor is using pre-made tools and scripts to grab databases… you do not represent the anti-sec movement, u are not allowed to greet underground groups like zf0, ab, h0n0, el8 like your member “AnonSabu†was doing, you will never be apart of the underground scene, if anyone thinks you are underground and can actually hack they have no idea about what happens in the underground scene. oh and TeaMp0isoN Issue 2 is coming out VERY soon exposing lulzsec members (pictures, addresses, passwords, ips,phone numbers etc). . . . not so anonymous anymore are you? lets hope that you can swim because the lulzboat just got titanic’d
Adding a little “humor,†a video clip of the song “My Heart Will Go On†from the movie Titanic was also posted. In addition, the group also stated that they will post the identities of every LulzSec member in the next issue of their magazine. So far, the Twitter account of LulzSec has remained quiet since the attack by TeaMp0isoN_.
You can check out a copy of the hacked site here for your own amusement.
Later, Sven Swootleg, the Dutch owner of the website hacked by TeaMp0isoN_ has denied that he is involved with LulzSec, and his statement can be found below.
This website was compromised through exploiting a plugin in an outdated WordPress setup, uploading a shell, and replacing the index page. I am not a member of Lulzsec (a statement I have made several times before in various places), noone “hacked the server†(this has been verified by the hosting company, as this website is on shared hosting) and this was definitely not an “elite hackâ€. I am not available for further comments to press.
How can we know that he’s telling the truth? The members of LulzSec are meant to stay anonymous, and he’s NOT going to publicly admit he’s affiliated with the group. However, who knows?
[via grindgadget]